Most teams building AI agents started with a webhook stack they already knew — Svix, Hookdeck, or a custom queue-based thing they built for a previous SaaS product. Those stacks work fine for classical webhook delivery. They start to feel awkward once the consumer is an agent instead of a classical API.
This post is for teams mid-migration, or considering one. What changes? What do you need that you didn't before? And how do you actually switch without breaking production?
Five mental-model shifts
1. Consumer non-determinism moves the reliability goalposts. A classical webhook consumer is deterministic — same input, same output, safe to retry. An agent is not — same input might make different tool calls, spend different tokens, return different text. The event layer has to do more work to keep the input reproducible because the consumer won't do it for you.
2. Multi-channel ingest isn't optional. Classical SaaS webhooks are almost always HTTP. Agents routinely need to accept email (a customer forwards an invoice), forms (a user submits a support ticket), and scheduled triggers (daily summary). Stacks built around HTTP-only assume this is an integration problem. For agent workflows, it's table stakes.
3. Destinations diversify. Classical delivery goes to an HTTP endpoint. Agent delivery often goes to a queue (SQS, EventBridge, Pub/Sub) or object storage (archival, memory). Stacks that assume destination = HTTP endpoint force you to write a relay service. Stacks with typed destinations let you skip that.
4. Replay determinism becomes critical. Classical retry is "call the endpoint again with the same payload." Agent replay is "run the same input through a potentially different agent version." That requires persisting the exact dispatch bytes — not regenerating them from the current config.
5. File relay is a first-class need. Agents process documents, images, and attachments constantly. Classical webhook stacks treat files as someone else's problem — the payload references a URL, the consumer fetches. Agents need signed, stable references because file URLs expire and agents sometimes run minutes after the trigger lands.
What to keep from your existing stack
- Ingest URLs and signing secrets — don't rotate unless you have to. Migrate the URL, leave the secret untouched so producers don't have to re-configure.
- Monitoring and alerts — whatever dashboards your team watches already, pipe the new event layer into them via Pro+ event drains.
- Idempotency conventions — if you're using
Idempotency-Keyalready, keep it. Hooksbase honors that header natively. - Audit history from the old system — don't try to re-emit it. Archive the old data. New deliveries land in Hooksbase going forward.
What to re-architect
Things that usually need a second pass during migration:
- Routing. If your current stack has custom middleware that dispatches to different agent versions, replace it with Hooksbase routing rules. Destinations + priority-ordered rules over payload/headers/provider is usually simpler than the middleware you have.
- Signature verification. For Stripe, GitHub, Clerk, Slack, and Resend, move provider-specific verification into Hooksbase provider packs after the request has passed Hooksbase ingest auth. For other providers, keep a small verification forwarder in front of Hooksbase.
- Retry policy. Classical stacks default to infrequent retries (exponential, capped at 24h maybe). Agents often need tighter retry on transient LLM errors and faster terminal failure for prompt/schema errors. Use Hooksbase custom retry policy (Starter+).
- DLQ workflow. If you're on a stack where DLQ means "SNS topic nobody watches," replace it with Hooksbase DLQ and Starter+ bulk re-drive once the agent is fixed.
- Observability. Pro+ streams of "agent event lifecycle" to Axiom or Datadog via Hooksbase event drains — usually richer than what the old stack emitted.
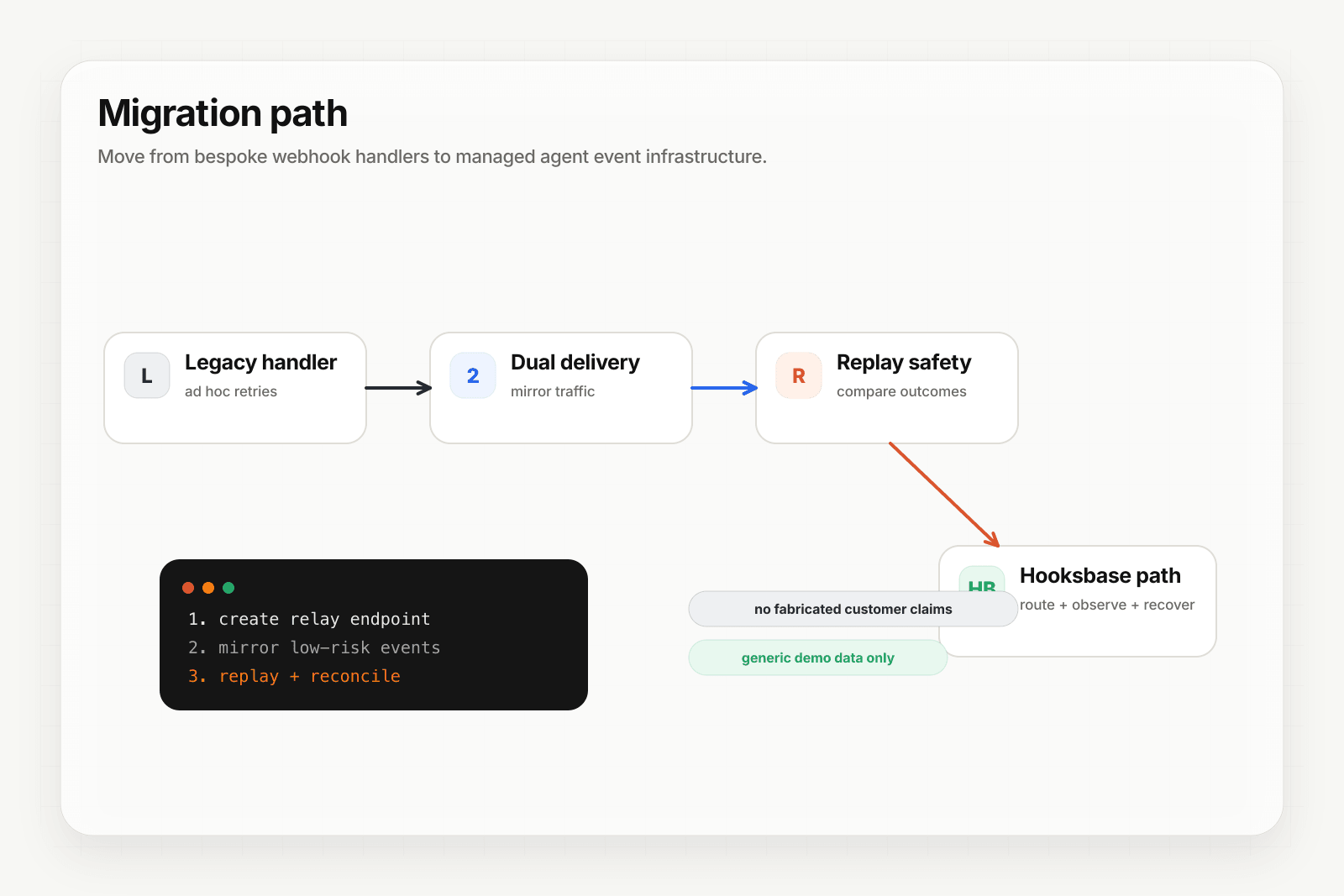
The switchover
For HTTP ingest, switchover is URL-level:
- Create the webhook in Hooksbase with your agent endpoint as the destination
- Dual-run: point one or two producers that can send Hooksbase ingest auth at the Hooksbase URL; use a forwarder for producers that cannot
- Verify deliveries are landing in both places and producing the same agent behavior
- Cut over remaining producers
- Decommission the old stack after a retention window
For email ingest, email forwarding rules handle it cleanly — forward the old address to the new Hooksbase address until senders update.
For forms, the embed URL changes. Update the form embed once, senders are automatically on the new endpoint.
Specific migration guides
Compare the two head-to-head: Hooksbase vs Svix · Hooksbase vs Hookdeck
The honest trade
There are cases where Svix or Hookdeck is the right call. If your consumer is classical SaaS, if you need on-prem or self-host, if per-event pricing at scale matters more than bundle pricing — go with the tool that fits.
Hooksbase makes sense when the consumer is an agent (or anything non-deterministic), when multi-channel ingest is on the roadmap, and when you'd rather buy a bundled product than a metered one. Most agent teams land in that column.